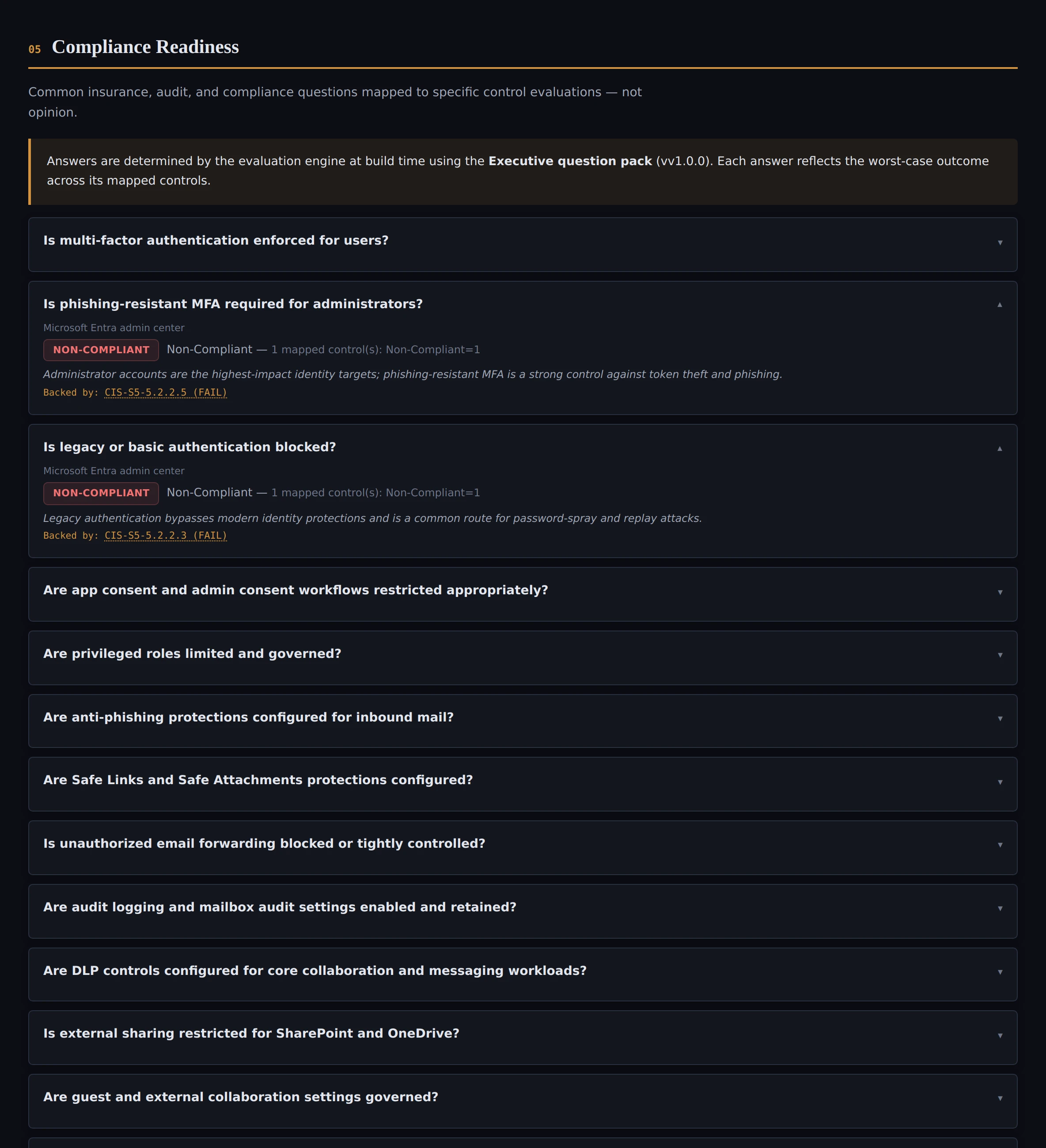
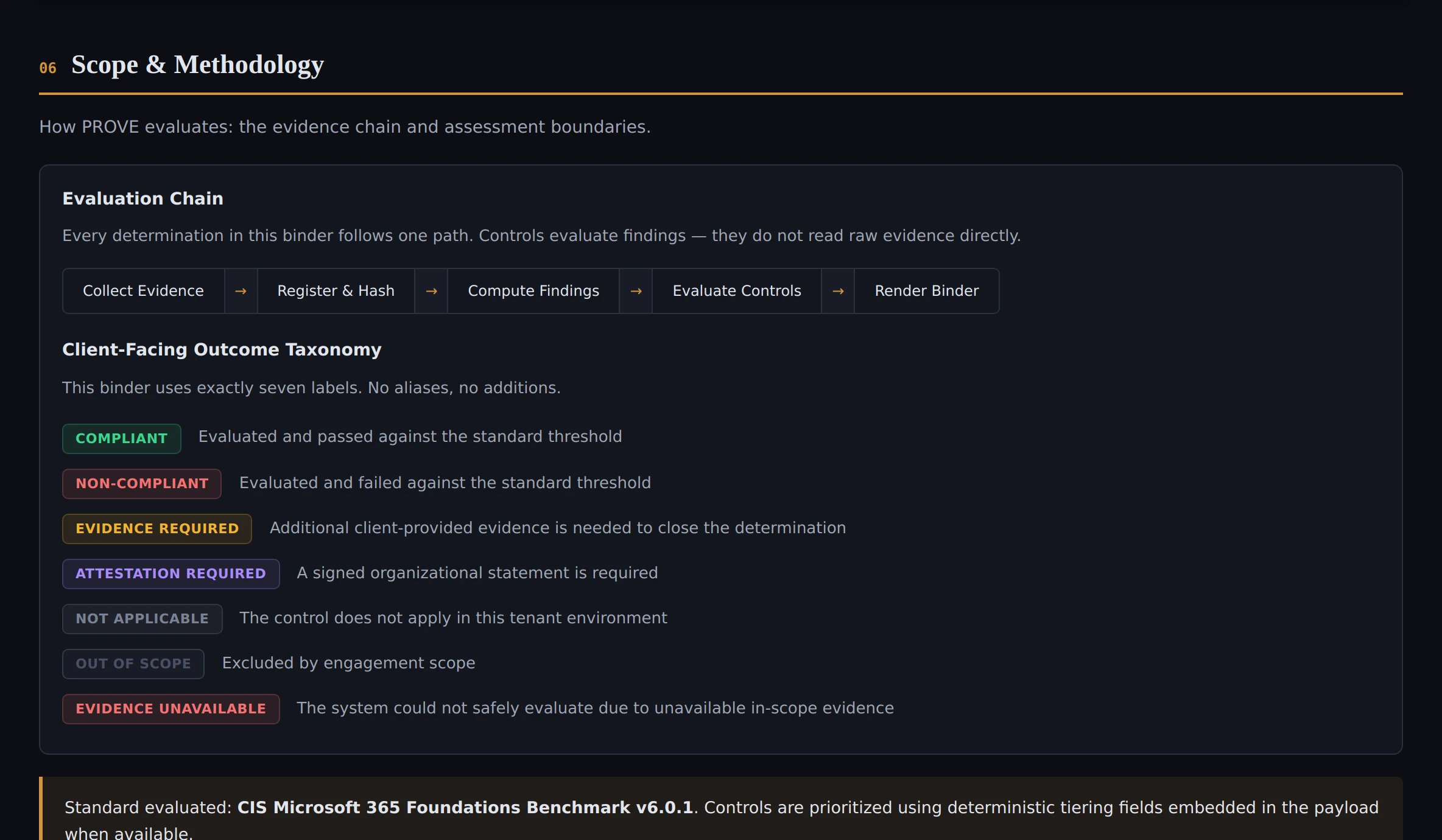
What exactly do you look at?
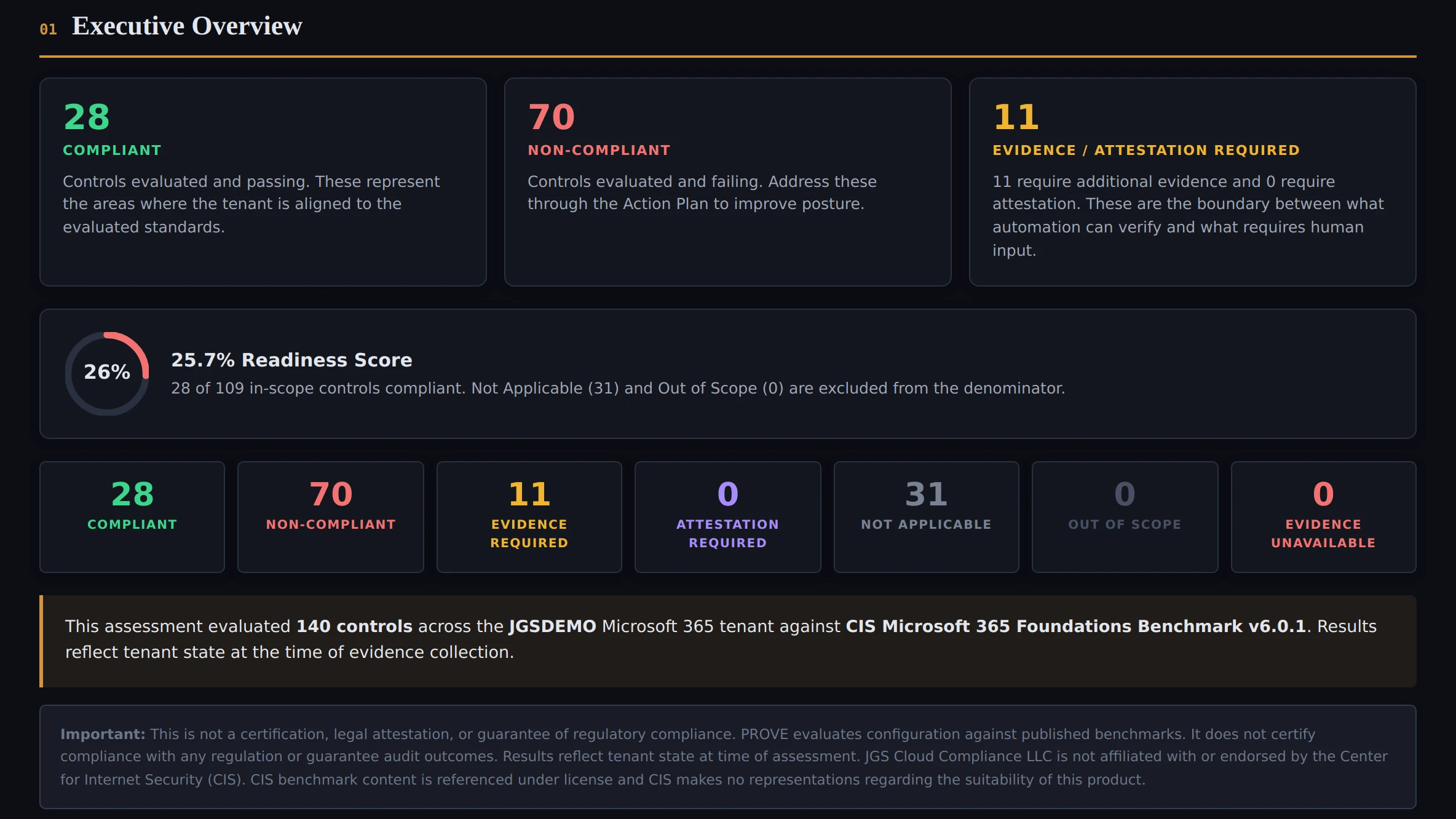
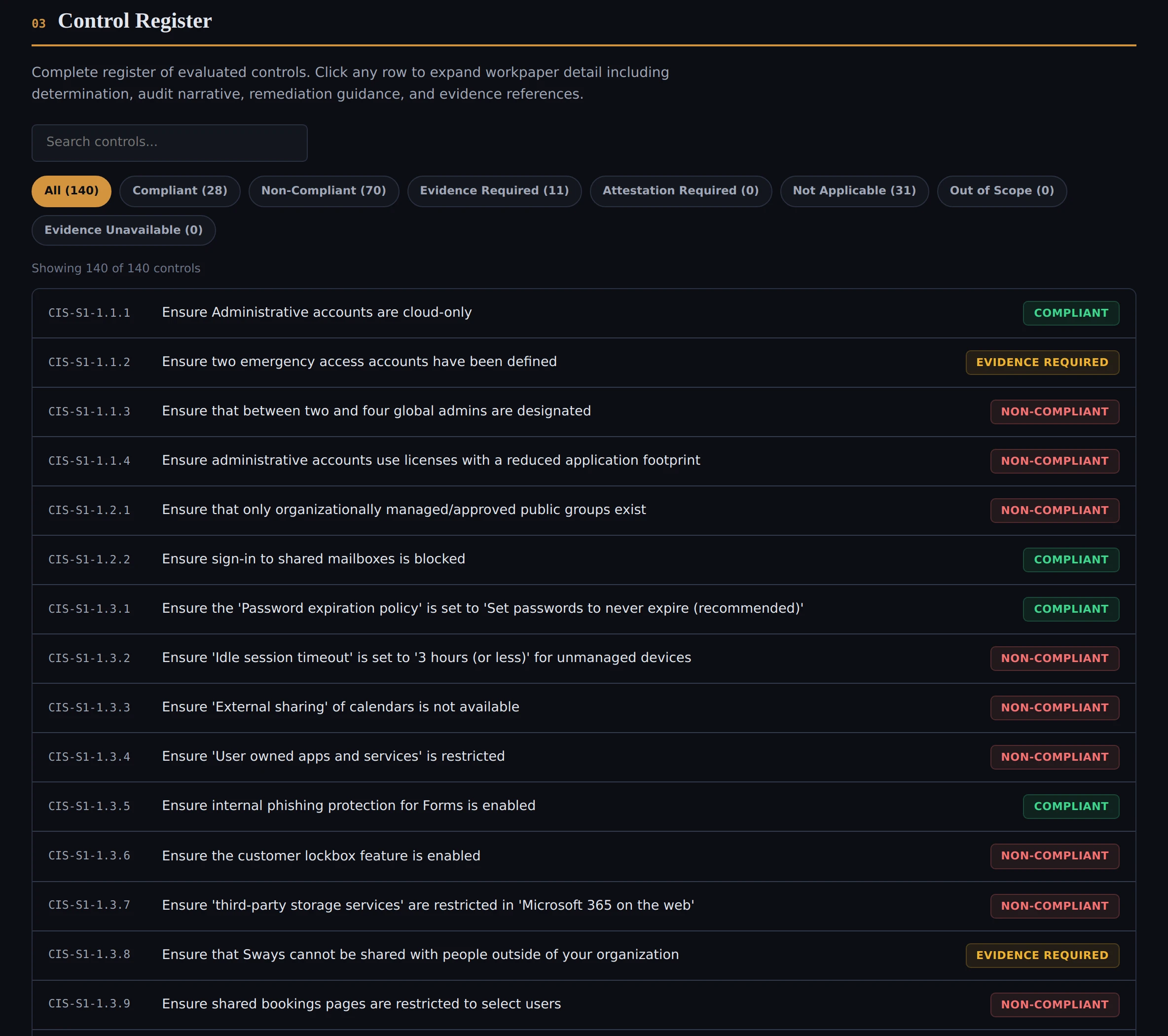
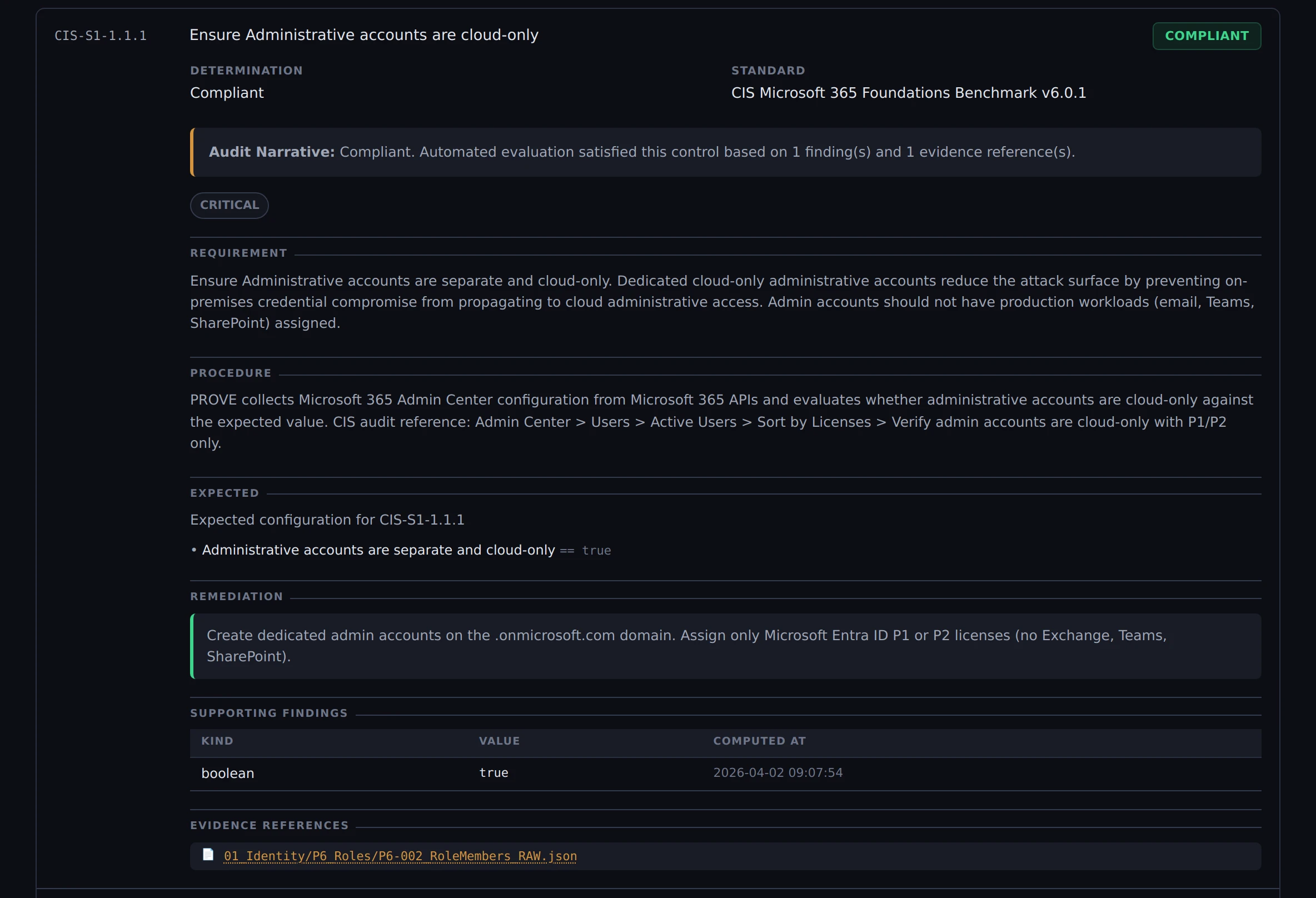
Nine CIS benchmark sections: Microsoft 365 admin center, Microsoft 365 Defender, Microsoft Purview, Microsoft Intune admin center, Microsoft Entra admin center, Exchange admin center, SharePoint admin center, Microsoft Teams admin center, and Microsoft Fabric. All read-only. We export evidence from Microsoft 365 admin APIs and evaluate it against the CIS Microsoft 365 Foundations Benchmark v6.0.1.
What access do you need?
A Global Admin or Privileged Role Admin clicks a one-time consent link that grants 35 scoped permissions across Microsoft Graph, Defender, Exchange, and SharePoint. Certificate-based authentication — no one stays signed in. SharePoint admin access is optional. You can revoke everything at any time by deleting the enterprise app from Entra ID.
Do you change anything in our Microsoft 365?
No. PROVE is “show me, don’t touch.” If you want changes afterward, that’s a separate engagement with its own approved scope.
How long does it take?
Evidence collection takes hours, not weeks. After the run, you receive your binder and worklists. The timeline depends mostly on scheduling and prerequisites, not the work itself.
We already use Secure Score / Defender dashboards. Why this?
Dashboards help you manage your environment day-to-day. But when someone outside your organization asks for proof, they need something they can read and verify independently—without logging into your tenant. That’s what the binder is.
Is this a certification?
No. PROVE produces evidence and governance determinations. It is not a certification, legal attestation, or guarantee. Auditors and underwriters apply their own judgment—we give them organized, verifiable evidence so that review goes faster.
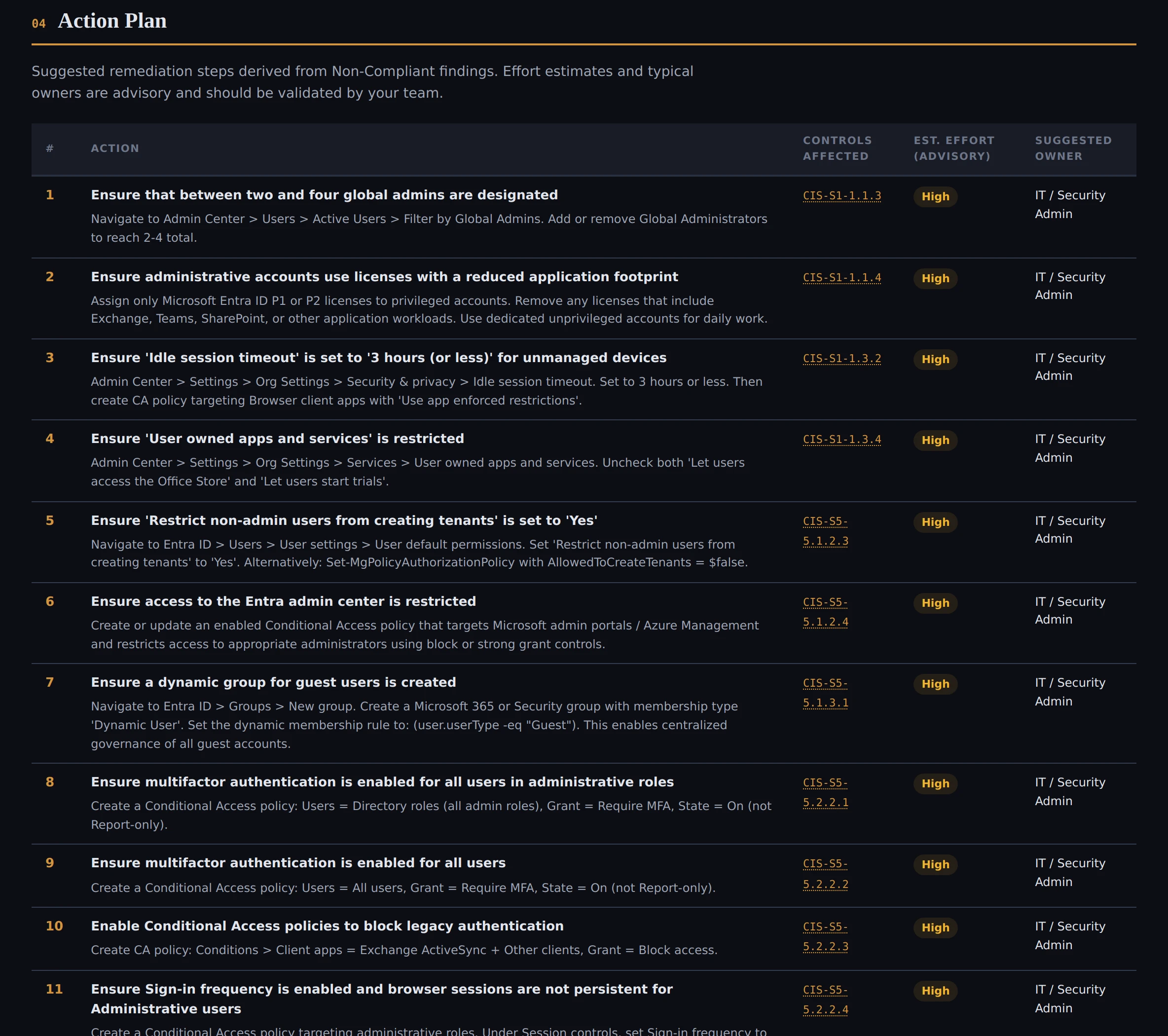
What if some items need follow-up?
They go on a worklist. Some controls require a policy document, a signed statement, or a manual export that a machine can’t pull automatically. Each worklist entry tells you exactly what to provide and what “done” looks like.
How are decisions made?
The evaluation engine is deterministic — rule-based logic applied to collected evidence. Same evidence in, same outcomes out.
How do we verify the results haven’t been tampered with?
The bundle includes SHA-256 checksums for every evidence artifact, a chain-of-custody manifest, and a gate report documenting 15 integrity checks that passed before delivery was allowed.
What happens to our data after the engagement?
Evidence is securely deleted within 30 days of final delivery. No cloud backups, no persistent store. Your binder is yours — you retain the full assessment package under your own data governance.